There's a Bug in VPC CNI v1.21.0 That Silently Drops All Traffic
A pointer aliasing bug in VPC CNI v1.21.0 caused namespace network policy rules to be written to the wrong eBPF map, leading to it dropping all traffic for every isolated pod.

Hi, I’m Orel.
I started this blog because I like making stuff, and I value authenticity.
Most of what we see online is heavily edited highlight reels - I wanted to be different.
This is where I share the things I build, opinions I have, and cool stuff I find out about.
On any given day that might be Kubernetes, a 3D print, an electronics project, or something else I broke and had to figure out how to fix.
A pointer aliasing bug in VPC CNI v1.21.0 caused namespace network policy rules to be written to the wrong eBPF map, leading to it dropping all traffic for every isolated pod.

How I reverse engineered the Electra AC app API using Genymotion and HTTP Toolkit, then built a web interface running on an ESP32-C3 SuperMini to control my AC from anywhere.

Reflecting on 2025 and setting my DevOps goals for 2026 - from automated workflows to learning a new language and beyond.

Learn how to build a mouseless workflow on macOS using KMonad for advanced keyboard remapping, including layers, aliases, and practical examples for eliminating mouse dependency.

Discover how to use Helm post renderers to modify Kubernetes manifests on the fly without changing chart source code, useful for quick fixes and edge cases.

Learn how to configure cross-account access for AWS SQS queues using resource-based policies and IAM permissions.

Reflections on how taking initiative and being willing to learn matters more than credentials or years of experience in building a successful tech career.

A comprehensive guide for IT professionals looking to transition into DevOps, covering essential soft skills like leadership and critical thinking, plus key tools including CI/CD, Kubernetes, IaC, and observability platforms.

Get started with Crossplane, the Kubernetes-native infrastructure as code tool, and learn how to provision AWS resources using Providers, CompositeResourceDefinitions, and Compositions.

An introduction to Karpenter, the Kubernetes node autoscaler that dynamically provisions and terminates nodes based on pod requirements, with practical EKS examples.

A deep dive into terminal escape codes, CSI and OSC sequences, and how to customize your Bash shell with vi-mode indicators and cursor styling.

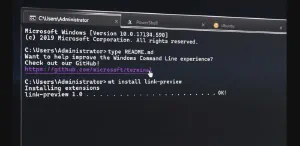
Resolve PowerShell cmdlet conflicts between modules like VMware PowerCLI and Hyper-V using the module-qualified cmdlet syntax.

Building a thermal receipt printer that prints Jira issues using Go, ESC/POS commands, webhooks, and SSH tunneling through an Azure Ubuntu server.

Get started with Kusto Query Language (KQL), Microsoft's powerful query language for Azure Log Analytics and Azure Data Explorer.

A guide to viewing Azure AD role definitions and their allowed operations using PowerShell, with examples for analyzing roles like Global Administrator.

How a blender warranty registration led to discovering a website security vulnerability that exposed customer personal data through predictable image URLs.

Learn how to set up your own Garry's Mod dedicated server on Google Cloud Platform using SteamCMD, with step-by-step configuration for server settings and game content mounting.

Learn how to migrate your WhatsApp stickers to Signal, including how sticker packs work under the hood and step-by-step instructions for importing them.

Understand Azure role definitions and their JSON structure, including Actions, NotActions, DataActions, and AssignableScopes for RBAC permissions.

Step-by-step guide to cloning a hard drive or SSD using Clonezilla, the free and open-source disk imaging solution.

An overview of Windows Terminal's features including multi-tab support, custom themes, keyboard shortcuts, panes, and why it could be a productivity game-changer for IT professionals.
An honest review of AWS WorkSpaces as a work-from-home solution, covering performance, security, and pitfalls of Amazon's Desktop-as-a-Service platform.

The difference between ;, &&, ||, and & in Linux — a practical guide to chaining bash commands with real-world examples.

Learn how to rename Active Directory user objects using PowerShell's Rename-ADObject cmdlet when Set-ADUser falls short.

Discover how to use Repadmin's showobjmeta option to inspect Active Directory object metadata, track attribute changes, and perform identity forensics across domain controllers.

Step-by-step guide to synchronizing your Active Directory users and groups with Google Cloud using GCDS, including tips for password sync and automated scheduling.

How to check a string against multiple regex patterns in Python — using map() when you need to know which patterns matched, or any()/all() for a quick boolean check.

How to customize keyboard layout switching shortcuts in Ubuntu using gsettings when gnome-tweaks causes focus issues.

A weekend project building a space invaders-style game on an Arduino with an 8x8 LED matrix, covering player movement, enemy spawning, and game logic in C++.

Step-by-step guide to enabling Active Directory auditing through Group Policy, covering both basic Local Policy options and advanced audit policy configuration.
